How to Audit Cross-Account Roles Using AWS CloudTrail and Amazon CloudWatch Events | AWS Security Blog

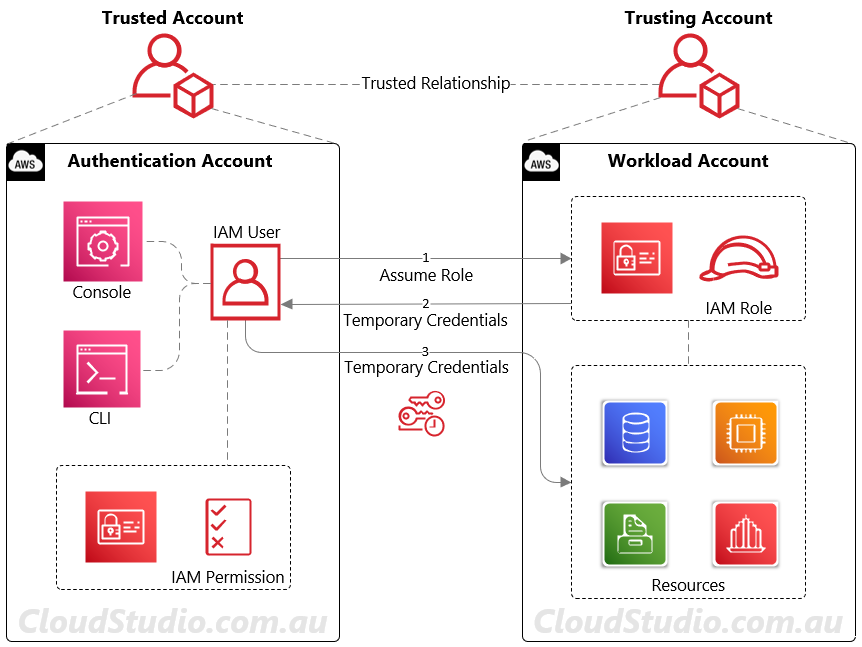
Confused Deputy Attack in IAM, Resource, and AssumeRole Policies | by Teri Radichel | Cloud Security | Medium
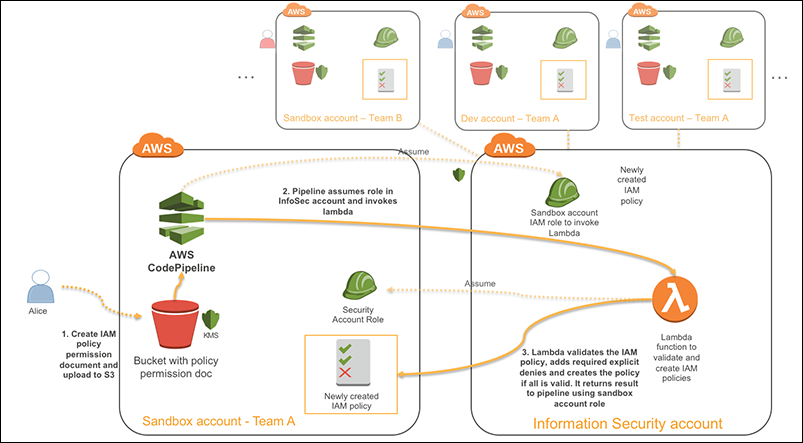
How to centralize and automate IAM policy creation in sandbox, development, and test environments | AWS Security Blog